The
Tough Sudoku of July 1, 2010 seemed like a fantastic puzzle to use to re-open this blog.
The main intent of this post is to further investigate the sudoku tip, trick or technique of
using Almost Continuous Loops.
It is common practice in advanced Sudoku solving to use Almost Locked Sets, which are a form of an Almost Continuous Loop. It is also a
common practice to use Almost Unique Rectangles, which is a grouping of Almost Continuous Loops from which one cannot resolve any of the internal members
of those loops. Since no resolution is possible inside that group of loops, such a grouping of Almost Continous Loops cannot exist in a single
solution Sudoku. The intent of this post is to not only look at these common Almost Continous Loops, but to also consider a few others.
Rather than solve the entire puzzle, this blog post will concentrate on a group of related moves that are available after only elementary moves
have been executed. Recognizing the power of Almost Continous Loops, in their many forms, is in my opinion an underutilyzed Sudoku technique.
If this is your first visit to this blog, welcome! Unfortunately, if you are a first time visitor, this page may seem
like it is written in a different language. Well, it is!! Previous blog pages may be helpful. Links to these pages are
found to the right, under Sudoku Techniques. The earliest posts are at the bottom, and if you have never perused
the intricacies of our special coded language here, you may wish to start close to beginning. The list is rather large, but you may
have some hope of understanding this page if you visit the
Definitions page.
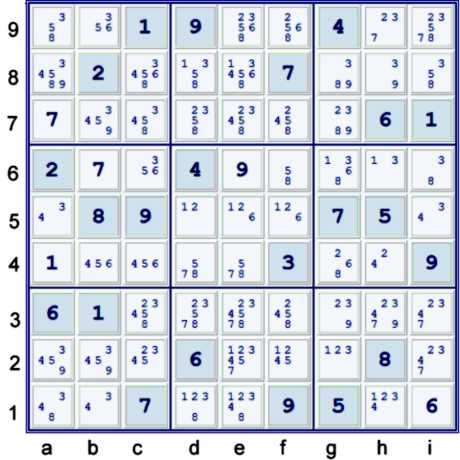
The Puzzle

Above, find the puzzle as given. A small handful of easy steps are available:
- (6)i1 % row & box - a naked single in both row and box
- (9)e6 % row, column & box
- (7)b6 % row
- (7)a7 % row
- NakedTriple(126)def5 => a5 ≠1, i5 ≠2, f6 ≠16, d4 ≠12, e5 ≠126
- (1)a4 % column & box - UP 27 (Unique Possibilites to 27 solved cells)
- LC(9)ab2 => g2 ≠9
This brings the puzzle to the state below, with the possibilities (pencil marks) shown.
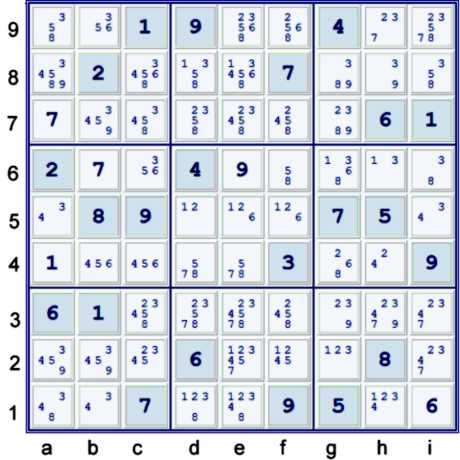
Puzzle after easy steps
A continuous loop
This puzzle has a number of interesting possible first moves. Many of these contain loops or
almost loops. Most of them involve candidates (126) primarily. Some other candidates may play minor
roles. One which I expect most advanced solvers would find is listed below:
- (1)g6 = g2 - f2 = (1-6)f5 = f9 - b9 = b4 - c6 = (6)g6 loop
- => e2 ≠1, e9,c4 ≠6, f5≠2, g6≠38
In a continuous loop, or continuous network, each strong link considered is proven also weak,
and each weak link considered is proven also strong. Thus, each set considered is proven to
contain exactly one of the elements of the set. For example, the contents of the cell f5 is proven
to contain exactly one of candidates (16). Clearly, f5 cannot contain both, and if it contained
neither, then one could argue that g6 must contain both (16), by simply following the chain out from
f5 in both directions.
Although using a continuous loop is very often a very nice way to start a puzzle, there is
a tendency for solvers to search for a step that will start to solve some cells. Unfortunately,
the loop shown above does not seem to further the puzzle significantly, at least not without some
help from some other steps. Regardless, the intent of this post is to look around at what else
might be available.
A pair of conflicting Uniqueness Loops
Some solvers consider Uniqueness derived steps to be the very best types of steps. Others disdain
them. The following step is quite ok regardless of which camp one favors. A set of conditions
which prevent a uniqueness condition from occuring must be true. Any set which must contain at
least one truth in it is called a Strong Inference Set (SIS). Consider the two
following possible Uniqueness conditions:
- AUR(12)de15 =>
- (12)h1 to avoid Hidden Pair - HP - (12) at de1.
- OR (6)e5 to avoid Naked Pair - NP - (12) at de5
- => SIS [(12)h1, (6)e5]
- Unique Loop (12)de15, (126)def5, (26)ef9 =>
- (12)h1 to avoid HP(12)de1
- OR (2)hi9 to almost avoid HP(26)ef9
- OR (6)e8 to almost avoid HP(26)ef9
- => SIS [(12)h1, (6)e8, (2)hi9]
- Considered together, these two items have a restricted common (6) column e. Thus,
since (6) cannot exist in both SIS listed above, it can be ignored in deriving a new SIS.
- These two items also have a common item in both SIS: (12)h1
- Considered together, these two uniqueness conditions =>
- SIS [(12)h1, (2)hi9]
If one does not like uniquneness, note that (1) limited to de8 => neither the AUR nor the Unique
Loop can exist. Thus, the same SIS are easily derived without considering Uniqueness.
If h1 is limited to (12), we would have a continuous loop - an XY Cycle:
- (1=2)h1 - (2=4)h4 - (4=3)i5 - (3=1)h6 loop
- => gi6≠3; h39≠2
Thus, one can write the chain using the AUR and Unique Loop derived SIS:
- (8=3)i6 - [XYCycle (12)h1,(24)h4,(34)k5,(31)h6] = (2)hi9 - (2)g7 = NT(389)g7gh8
- => g46,i89≠8
- => two singles
In Sudoku, there are often many ways to reach the same or similar conclusions. I found at least
two here that bear examination. The more tricks in the tool bag, the better chance of finding
such steps.
For reference, here is the puzzle again after easy steps
A series of almost continuous loops
But for (2)f7, one would have the following continous loop:
- (2)h1 = de1- f23 = HP(26)f59 - HP(61)f59 = (1)f2 - de1 = (1)h1 Loop
- => the following candidates could be removed: (58)f9, (12)e2, (2) de3, (34)h1
- => XY cycle noted previously
Therefor, one can write the following chain:
- (8=3)i6 - [XYCycle (12)h1,(24)h4,(43)i5,(31)h6] = (34)h1 -
- [(2)h1 = de1- f23 = HP(26)f59 - HP(61)f59 = (1)f2 - de1 = (1)h1 Loop]
- = (2)f7 - g7 = NT(389)g7gh8 =>
- h46,i89≠8
This step seems a bit less presumptive than the one using Uniqueness, but is fairly complex. However,
it does illustrate how
continuous loops can be used in chains.
A simpler way to reach the same conclusion - Almost XWings
Consider (2) in columns cfi. Since (2)c is limited to c23, at most one of i23, f23 can contain (2).
This logic is precisely analgous to Almost Locked Sets. Thus, one can immediately write the
SIS: (2)[i9,f579]. One can partition this SIS in any way which one wishes. Since (6)f is already
limited to f59, and since (2)i9f7 have a common target - (2)g7 - the following chain almost
writes itself:
- NT(839)g7gh8 = (2)g7 - (2)f7,i9 = HP(26-61)f59 = (1)f2 - de1 = h1 - (1=3)h6 - (3=8)i6
- => g46,i89≠8; h9≠3
If one does not like to use derived SIS, one can use the corresponding Fish:
(2)cfi(237)i9Finned
SwordFish = (2)f59 rather than the derived SIS in the chain.
This latter step would be a likely first step, as it is less complex and gets an extra elimination.
For reference, here is the puzzle yet again after easy steps
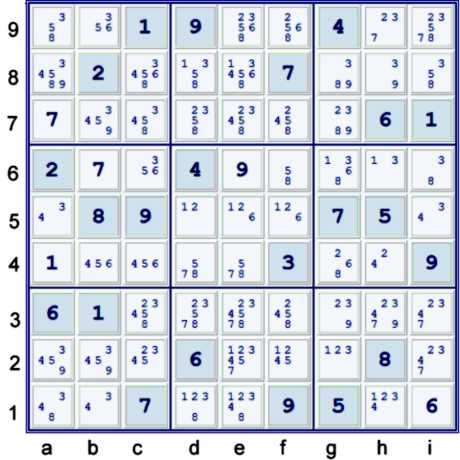
A large continuous loop with an Internal not quite continuous segment
This next potential first step is more complex, but imo the type of step often required for
true monster type puzzles. This puzzle is not one of those, but it does not hurt to point out
the possible step.
But for the (8) at g4, one would have the following chain:
- (6)e8 = c8 - c6 = g6 - (6=2)g4 - (2=4)h4 - i5 = a5 - (4)a8 = HP(46)ce8
- => e8≠1358
That almost chain by itself is not an almost continuous loop. The endpoints, HP(46)ce8 and (6)e8
are not in conflict with each other. However, that endpoint - e8 - forms a potential Hub for
a loop. With the work done above, this large continous network almost writes itself:
- [(6)e8 = c8 - c6 = g6 - (6=2*)g4 - (2=4)h4 - i5 = a5 - (4)a8 = HP(46)ce8]
- = (8*)g4 - (8=3)i6
- - [XYCycle (12)h1,(24)h4,(43)i5,(31)h6]
- = HP(12)de1 - (38)d1 = NP(12)d15 - (1)d8 = (1)e8 Loop
- => the following are eliminated: (358)e8, (2)d37, (348)e1, (2)h39, (38)g6
The first line of this chain - in brackets - must be treated as a whole, and one cannot prove
any of the internal weak links strong in that line. However, the weak links outside of that line
are proven strong. Although this loop is interesting, if one eliminates (8)g4 by one of the other
proposed first steps, all the other conclusions, plus a few more, will follow.
This concludes my investigation into initial almost continuous loops in this puzzle. There
are certainly few more. If I were to try to solve this puzzle, below is a possible path:
- Start 22 UP 26; LC(9)ab2 => g2≠9; NT(126)def => ai5,de4,f6≠126; UP 27
- NT(839)g7gh8 = (2)g7 - FSFc23f237,i239 = HP(26-61)f59 = (1)f2 - de1 = h1 - (1=NP38)hi6
- => g46,i89≠8; h9≠3; UP 29
- (6)e8 = c8 - c6 = g6 - (6=2)g4 - (2=4)h4 - i5 = a5 - (4)a8 = HP(46)ce8
- => e8≠1358; UP 31; HP(12)eh1
- (8)a1 = d1 - (8)f3 = WWing(24)f3h4,(2)eh1 - (4)h3 = h4 - i5 = a5 => a1≠4; UP 32
- (8)f3 = WWing(24)f3h4,(2)eh1 - (4)h3 = (4-2)h4 = (2-1)h1 = e1 - f2 = HP(16)e59 => e9≠8
- XYZ type Chain: - considers locations of (3) column b: - kraken (3)b:
- HP(93*)gb7 = [(2=6)g4 - b4 = (6-3*)b9 = (3*)b2 - g2 = NP(12)g2h1 - i23 = (2)i9]
- => g7≠2 => LC(2)hi9 => ef9≠2; UP 81